The errors, or rather defects in the jargon, that a static analysis tools produce can be considered low cost well formed bug reports available very early in the development process.
When I say low cost it is because they can be found by a machine without a user or fellow developer wasting their time finding them. Well formed comes because the machine can describe exactly how it came to the logical deduction leading to the defect.
Introduction
Static analysis is in general terms using the computer to examine a program for logic errors beyond those of pure syntax before it is executed. Examining a running program for defects is known as dynamic program analysis and while a powerful tool in its own right is not the topic of discussion.This analysis has historically been confined to compiled languages as their compilers already had the Abstract Syntax Tree (AST) of the code available for analysis. As an example the C language (released in 1972) had the lint tool (released in 1979) based on the PCC compiler.
Practical early compilers (I am generalising here as the 19070s were a time of white hot innovation in computing and examples of just about any innovation in the field could probably be found) were pretty primitive and produced executables which were less good than hand written assembler output. Due to practical constraints the progress of optimising compilers was not as rapid as might be desired so static analysis was largely used as an external process.
Before progressing I ought to explain why I just mixed the concept of an optimising compiler and static analysis. The act of optimisation within those compilers requires program analysis, from which they can generate defect reports which we all know and love as compiler warnings, also explaining why many warnings only appear at higher optimisation levels where deeper analysis is required.
The attentive reader may now enquire as to why we would need external analysis tools when our compilers already perform the task. The answer stems from the issue that a compiler is trying to reconcile many desirable traits including:
- Produce correct (expected) output from the source code for the target processor
- Produce output which will execute using the smallest amount of resources possible (not just CPU time but memory access and cache usage)
- Generate output in a reasonable amount of time.
- Have a reasonable cost (both developer time and research into new methods) to implement the compiler itself.
- Produce useful diagnostics
The slow progress in creating optimising compilers initially centred around the problem of getting the compiled output in a reasonable time to allow for a practical edit-compile-run-debug cycle although the issues more recently have moved more towards the compiler implementation costs.
Because the output generation time is still a significant factor compilers limit the level of static analysis performed to that strictly required to produce good output. In standard operation optimising compilers do not do the extended analysis necessary to find all the defects that might be detectable.
An example: compiling one 200,000 line C program with the clang (v3.3) compiler producing x86 instruction binaries at optimisation level 2 takes 70 seconds but using the clang based scan-build static analysis tool took 517 seconds or more than seven times as long.
Using static analysis
As already described warnings are a by-product of an optimising compilers analysis and most good programmers will endeavour to remove all warnings from a project. Thus almost all programmers are already using static analysis to some degree.
The external analysis tools available can produce many more defect reports than the compiler alone as long as the developer is prepared to wait for the output. Because of this delay static analysis is often done outside the usual developers cycle and often integrated into a projects Continuous Integration (CI) system.
The resulting defects are usually presented as annotated source code with a numbered list of logical steps which shows how the defect can present. For example the steps might highlight where a line of code allocates memory from the heap and then an exit path where no reference to the allocated memory is kept resulting in a resource leak.
The level of erroneous defect reports varies depending on the codebase being analysed and how good the analysis tool being used is. It is not uncommon to see false positive rates, even with the best tools, in excess of 10%
Good tools allow for this and provide ways to supply additional context through model files or hints in the source code to suppress the incorrect defect reports. This is analogous to using asserts to explicitly constrain variable values or a type cast to suppress a type warning.
Even once the false positives have been dealt with there comes the problem of defects which while they may be theoretically possible take so many steps to achieve that their probability is remote at best. These defects are often better categorized as a missing constraint and the better analysis tools generate fewer than the more naive implementations.
An issue with some defect reports is that often defects will appear in a small number of modules within programs, generally where the developers already know the code is of poor quality, thus not adding useful knowledge about a project.
As with all code quality tools static analysis can be helpful but is not a panacea code may be completely defect free but still fail to function correctly.
Defect Density
A term that is often used as a metric for code quality is the defect density. This is nothing more than the ratio of defect to thousands of lines of code e.g. a defect density of 0.9 means that there is approximately one defect found in every 1100 lines of code.The often quoted industry average defect density value is 1, as with all software metrics this can be a useful indicator but should not be used without understanding.
The value will be affected by improvements in the tool as well as how lines of code are counted so is exceptionally susceptible to gaming and long term trends must be treated with scepticism.
Practical examples
I have integrated two distinct static analysis tools into the development workflow for the NetSurf project which I shall present as case studies. These examples show a good open source solution and a commercial offering highlighting the issues with each.Several other solutions, both open source and commercial, exist many of which have been examined and discarded as either impractical or proving less useful than those selected. However the investigation was not comprehensive and only considered what was practical for the project at the time.
clang
The clang project is a frontend to the LLVM project providing an optimising compiler for the C, C++ and objective C languages. As part of this project the compiler has been enhanced to run a collection of "checkers" which implement various methods of analysis on the code being compiled.The "scan-build" tool is provided to make the using these features straightforward. This tool generates defect reports as a series of html files which show the analysis results.
Because the scan-build takes in excess of eight minutes on powerful hardware the NetSurf developers are not going to run this tool themselves as a matter of course. To get the useful output without the downsides it was decided to integrate the scan into the CI system code quality checks.
Whenever a git commit happens to the mainline branch and the standard check build completes successfully on all target architectures the scan is performed and the results are published as a list of defects.
The list is accessible directly through the CI interface and also incorporates a trend graph showing how many defects were detected in each build.
Each defect listed has a detail link which reveals the full analysis and logic necessary to cause the defect to occur.
Unfortunately even NetSurf which is a relatively small piece of software (around 200,000 lines of code at time of writing) causes 107 defects to be emitted by scan-build.
All but 25 of the defects are however "Dead Store" where the code has a value assigned but is never checked. These errors are simply not interesting to the developers and are occurring in code generated by a tool.
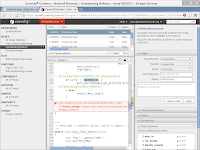
Of the remaining defects identified the majority are false positives and several (like the example in the image above) are simply improbable requiring a large number of steps to reach.
This shows up the main problem with the scan-build tool in that there is no way to suppress certain checks, mark defects as erroneous or avoid false positives using a model file. This reduces the usefulness of these builds because the developers all need to remember that this list of defects is not relevant.
Most of the NetSurf developers know that the project currently has 107 outstanding issues and if a code change or tool improvement were to change that value we have to manually work through the defect list one by one to check what had changed.
Coverity
The coverity SAVE tool is a commercial offering from a company founded in the Computer Systems Laboratory at Stanford University in Palo Alto, California. The results of the original novel research has produced a good solution which improved on analysis tools previously available.The company hosts a gratis service for open source projects, they even provide scans for the Linux kernel so project size does not appear to be an issue.
The challenges faced integrating the coverity tool into the build process differed from clang however the issue of execution time remained and the CI service was used.
The coverity scanning tool is a binary executable which collects data on the build which is then submitted to the coverity service to be analysed. This tool obviously relies upon the developer running the executable to trust coverity to some degree.
A basic examination of the binary was performed and determined the executable was not establishing network connections or performing and observably undesirable behaviour. From this investigation the decision was made that running the tool inside a sandbox environment on a CI build slave was safe. The CI system also submits the collected results in a compressed form directly to the coverity scan service.
Care must be taken to only submit builds according to the services Acceptable Use Policy which limits the submission frequency of NetSurf scans to every other day. To ensure the project stays within the rules the build performed by the CI system is manually controlled and confined to a subset of NetSurf developers.
 The results are presented using the coverity connect web technology based defect management tool. Access to the coverity connect interface is controlled by a user management system which precludes publicly publishing the results within the CI system.
The results are presented using the coverity connect web technology based defect management tool. Access to the coverity connect interface is controlled by a user management system which precludes publicly publishing the results within the CI system.Unfortunately NetSurf itself does not currently have good enough JavaScript DOM bindings to support this interface so another browser must be used to view it.
Despite the drawbacks the quality of the analysis results is greatly superior to the clang solution. The false positive rate is very low while finding many real issues which had not been previously detected.
The analysis can be enhanced by use of collection configuration and modelling files which remove intended constructions from consideration reducing the false positive rate to very low levels. The ability to easily and persistently suppress false positives through the web interface is also available.
The false positive management capabilities coupled with a user interface that makes understanding the defect path simple make this solution very practical and indeed the NetSurf developers have removed over 50 actual issues within a relatively short period since the introduction of the tool.
Not all of those defects could be considered serious but they had the effect of encouraging deeper inspection of some very dubious smelling source.
Conclusions
The principle conclusions of implementing and using static analysis have been:- It is a powerful tool which aids programmers in improving their software.
- It is not a panacea and bad code can have no defects.
- It can suggest possible defects early in the development cycle.
- It can highlight possibly problematic areas well before they affect a programs users.
- The tool and the infrastructure around it have a large impact on the usefulness of the results.
- The way results are presented has disproportionately significant impact on the usability of the defect reports.
- The open source tools are good, and improving, but coverity currently provides a superior experience.
- Integration into a projects CI system is beneficial.
When I started looking at this technology I was somewhat dubious about its usefulness but I have definitely changed my mind. It is a useful addition to any non-trivial project and the return on time and effort should be repaid handsomely in all but already perfect code (if you believe you have such code I have a bridge to sell you).




Very interesting. Coming from a safety-critical background, I am a big fan of static analysis, and I was not aware that the open source tools had come this far.
ReplyDeleteYes, I am agree with you Jon Ward.
ReplyDeleteSitus Poker Online
Agen Poker Online
Poker Online Indonesia
Bandar Ceme
99 Domino Online
Situs Poker Online
Poker Online terpercaya
Bandar Poker Online
Hello friend
ReplyDeleteYour post very nice and interesting,thanks for share with us. We offers online photo print and Superior Photo Scanning Service, If you are not satisfied with our service, we will refund your money.
very interesting ^-^
ReplyDeleteDaftar Akun Bola
Bandar Togel Online
IDNPLAY POKER
Daftar Livepoker
Livechat Livepoker
Casino Online
Daftar Domino QQ
Daftar Bandar Ceme
Daftar Capsa Susun
Your writing style is engaging and easy to follow. I didn't get bored while reading the post. http://www.sidingrichmondbc.com
DeleteThis comment has been removed by the author.
ReplyDeleteThanks for sharing this. Nice informative and helpfull.We are the largest alkaline water machine manufacturers in India. if you are looking alkaline water machine then
ReplyDeletevisit us:
alkaline water machine
techymax
ReplyDeleteIn this sense, an error analysis is present from the creation of the alphabet to a piece designed to be able to decipher the message in Open here fore more
ReplyDeleteThanks for sharing this great post. Site
ReplyDeleteAwesome information, I like the content really great. https://federalprocessingregistry.com
ReplyDeleteGlad to see this site again. Check here
ReplyDeleteThis is great information you've shared here. medicinehattowing.ca/
ReplyDeleteFeeling good to read such a informative blog, mostly i eagerly search for this kind of blog. I really found your blog informative and unique, waiting for your new blog to read. We offers multipl digital marketing service:
ReplyDeleteDigital marketing Service in Delhi
SMM Services
PPC Services in Delhi
Website Design & Development Packages
SEO Services Packages
Local SEO services
E-mail marketing services
YouTube plans
I do agree with this. Definitely a way for us to improve.
ReplyDeletehttps://buyguitarstrings.com
Sweet spot for us to improve and be better.
ReplyDeletehttps://mkminerals.com/
Definitely true! I agree with your point sir. It shape me actually to think the best decision! cheap towing greenville nc
ReplyDeleteThanks for sharing this great information. About us
ReplyDeleteVery informative! the best cbd creams
ReplyDeleteGreat post! Thanks for the share. yycsepticservices.ca/
ReplyDeleteYahooo! I'm impressed with your details here. Thanks | scottkeeverseo.com/
ReplyDeleteThanks for this great information you shared. Check us out
ReplyDeleteYaas! this is so great. Thanks | https://applicationfiling.com/
ReplyDeleteError analysis includes the activities of preventing, detecting errors, of recording errors singly and across projects, and of analyzing single errors and error data collectively. The purpose of error analysis is to provide assurance of the quality of high integrity software. https://www.shopedc.com
ReplyDeleteBeneficial post, you have added very useful content audience will be loving your upcoming write-ups in such a wave. We are also trusted as the mobile app development company head to us for more assistance in the IT field. Also visit: web application development company
ReplyDeleteHey, I really like this blog and it was very helpful for me to thank you so much. Also, check out our blog.
ReplyDeleteBombSquad MOD APK
Ohh it needs backup! Thanks go here
ReplyDeleteProgrammers have so much to thank for because of this analysis. https://online-application.org/social-security-cards/lost/
ReplyDeleteThanks for sharing this great article. Link here
ReplyDeleteIn India many types of smartphones is available. But middle class family can't afford expensive phones, because of low budget of family. That's why they can't use extra advance features. We will tell you about some smartphones, which under in your budget. Redmi 9i , OPPO A1K , Vivo Y11. Some smartphones is manufactured by India in very low budget Lava Z66, Mi Redmi 6A , Lenovo A7 , Lava Z2 , Vivo Y91i , OPPO A15 , Redmi 9A.
ReplyDeleteThank you for sharing this nice blog. Link here
ReplyDeleteGreat material
ReplyDeleteBirmingham Window Cleaner
On point article http://www.hendersonvilleroofer.com
ReplyDeleteGlad to check this site again. https://www.fortworthconcreteservice.com/
ReplyDeleteThanks for taking the time in sharing this post. Visit us here
ReplyDeleteI love the way you write and share your idea! Very interesting and different! Keep it coming! plumber
ReplyDeleteGlad to see this great blog. https://www.roofingprospembrokepines.com
ReplyDeleteReally great topics here to learn from, thanks! https://www.hvacfontana.com
ReplyDeleteReally great topics here to learn from, thanks! www.hvacfontana.com
ReplyDeleteExcellent information on your content, thank you for taking the time to share with us. Hendersonville House Cleaners
ReplyDeleteI read your work frequently and I just thought I'd say keep up the amazing work http://www.hendersonvilletnplumber.com
ReplyDeleteI really like reading articles that cause people to think. Also, thank you for allowing me to comment!
ReplyDeletehttp://www.concretehialeah.com
Such an impressive share! It is well-written and contains all the info, your Post is very unique and all information is reliable for new readers. http://www.winstonsalemplumbingprofessional.com
ReplyDeleteThanks for this great blog. Link here
ReplyDeleteYou guys are doing a great job. Thank you, and keep it up! Concrete Contractor in Houston, TX
ReplyDeleteGlad to see this awesome blog. weddingplannersraleigh.com
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteBecause of this delay static analysis is often done outside the usual developers cycle and often integrated into a projects Continuous Integration system. As a drywall installer, I'm happy that all these issue is now fixed.
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteThank you for this blog post, such an informational one and would help a lot to understand the static analysis.Pumba
ReplyDeleteI wanted to thank you for this excellent read!! I definitely loved every little bit of it. I have you bookmarked your site to check out the new stuff you post. Anthony Dietrich Gainesville VA
ReplyDeleteI'm impressed with your details here. Thanksfoundation contractors
ReplyDeleteRead More About Our Residential Tree Care & Lawn Care Services in Tuscaloosa AL. Visit our website tuscaloosatreeremoval.com/
ReplyDeleteWow! your data is very impressive. Thanks | amicosecurity.com/
ReplyDeleteGreat post i must say and thanks for the information. Education is definitely a sticky subject. However, is still among the leading topics of our time. I appreciate your post and look forward to more. Anthony Scott Dietrich
ReplyDeleteClayton Roofing Contractor offers affordable Emergency Roof Repair in Clayton, NC area. - Read more
ReplyDeleteAffordable Tree care Services In New Port Richey, FL. - Learn more
ReplyDeleteA tree removal need to be done by a by a tree care specialist, What are you waiting for. Call us now or book online at nampa-tree-service.com
ReplyDeleteMarvelous post. I'm a normal drop-in of your blog and appreciate you taking the time to maintain the excellent locus. I ’ll be a frequent drop-in for a long time.
ReplyDeleteMore info:Lean manufacturing operational excellen
This was an excellent article. Thank you for sharing it.
ReplyDeleteNordVPN
ReplyDeleteI hope this post is beneficial for viewers. Many thanks for the shared this informative and interesting post with us.
plagiarism-checker-x
Great article, it seems like we can all benefit from this, thanks drywall services
ReplyDeleteThis is really a big and great source of information. Thanks for sharing these information with all of us. Kinemaster Gold
ReplyDelete
ReplyDeleteWavePad Sound Edito Crack
VueScan Pro 9 Crack
allcrackfile.com
keygen4pc.com
That's an outstanding piece of work!I look forward to seeing more!I am very impressed form it.
ReplyDeleteeditplus 토렌트
easy cut studio High screen time creates many health problems like backaches, eyesight related problems, etc
ReplyDeleteimindmap crack latest 1 : to institute (something, such as a law) permanently by enactment or agreement. 2 obsolete : settle sense 7. 3a : to make firm or stable. b : to introduce and cause to grow and multiply establish grass on pasturelands. 4a :
ReplyDeleteconsoleact download Social media websites can operate as both curses and blessings in our modern society. The difference between it as a curse and a blessing all hangs on the shoulders of its users.
ReplyDeleteYou have done great article work. Your website is extremely useful. Kindly keep us informed about your work.
ReplyDeleteFree YouTube Download Crack
This is a good post. This post contains real quality information. We will definitely look into it. Really very useful tips are provided here. Thanks a lot. Keep up the good business. Thanks again for the great post. In my opinion, you will be a great blogger in the future.
ReplyDeleteavast cleanup premium serial key
This is a good post. This post contains real quality information. We will definitely look into it. Really very useful tips are provided here. Thanks a lot. Keep up the good work. Thanks again for the great post. In my opinion, you will be a great blogger in the future.
ReplyDeletemicrosoft office 2013 full crack
Good material. Good job, see you dear, thank you very much for such a good job. I would like to thank you for this post. Here are some useful links for students around the world. These tips may help me in the future. A high-profile publication with all the essential information.
ReplyDeletedeepl pro crack
Love this post. I had realize a lot of things. Thanks for sharing inspiration. landscaperfresnoca.com/
ReplyDeleteYou have a nice blog so far. Thanks https://www.change-of-address-form-online.com
ReplyDeleteI've been following your blog for a while, and your content never disappoints. Keep up the excellent work! Burnaby Roofing Contractor
DeleteThanks for the improvement. Keep it up.
ReplyDeleteSanta Barbara Electrician
EasyWorship 7 Crack
ReplyDeleteActive Partition Recovery Ultimate
JDownloader Crack
UsbFix Crack
Mask My IP Crack
Adobe Master Collection CC 2019
Adobe Master Collection CS3
Cyberlink YouCam
Find Ivy Bronx TV Cabinet, Black tv stand with led lights, Can Accommodate 55-Inch TV Screen,Black reviews & recommendations from people you can trust.
ReplyDeleteError analysis is a method used to document the errors that appear in learner language, determine whether those errors are systematic, and (if possible) explain what caused them.
ReplyDeleteCheck out more here
An error analysis should focus on errors that are systematic violations of patterns in the input to which the learners have been exposed. Find out more info at www.newportbeachtreeservice.com/
ReplyDeleteExamples in this category are spills, misreading a device such as a burette, misinterpretation of the procedure, incorrect handling of a micro-pipettor, and forgetting to rinse out a beaker when doing a quantitative transfer. These errors are known and easily preventable, if the experiment is repeated. Check out more info here.
ReplyDeleteErrors are the difference between the true measurement and what we measured. We show our error by writing our measurement with an uncertainty. See more info about Tree Service Orange County
ReplyDeleteThank you for the information. Pool fence fort myers
ReplyDeleteGreat blog. Fence installation tampa
ReplyDeleteNice blog. Concrete contractors colorado springs co
ReplyDeleteFence companies in maryland
ReplyDeleteFor home inspection services in raleigh, click here
ReplyDeleteGreat blog. Click here for best Wood fence installation in raleigh services.
ReplyDeleteDefinition. Error analysis is a branch of applied linguistics. Find the best Harrisonburg Tree Service Company
ReplyDeleteThis is true. Errors are helpful in every way as you will end successful. For more details check out Tree Removal Spokane.
ReplyDeleteI guess I am the only one who came here to share my very own experience. Guess what!? I am using my laptop for almost the past 2 years, but I had no idea of solving some basic issues. I do not know how to Crack Softwares Free Download But thankfully, I recently visited a website named ProCrackHere
ReplyDeleteDeepL Pro Crack
Ashampoo Uninstaller Crack
Thanks for sharing such a great post. Nice Post I Enjoyed!
ReplyDeleteDeepL Pro Crack
Zoom Player MAX Crack
CCleaner Professional Crack
Error analysis is a very important area of applied linguistics as well as of second and foreign language learning. Check also about Spokane HVAC Installation
ReplyDelete
ReplyDeleteI guess I am the only one who came here to share my very own experience. Guess what!? I am using my laptop for almost the past 2 years, but I had no idea of solving some basic issues. I do not know how to Download Latest PC Cracked Softwares But thankfully, I recently visited a website named pcsoftz.net
DeepL Pro Crack
Glad to found this. Thanks for sharing. www.fencecompaniesstpetersburgflpros.com
ReplyDeleteI think am only the person who share my own experience
ReplyDeleteNo doubt the blog is written perfectly and lot of information
but i have something more for all of you
if you want to download the premium games for free without any cost simply download it for free
silhouette studio CafecrackSilhouette Studio Crack Designer Edition that allows users to upgrade. Diagram Studio programming allows you koikatsu fitpcgames to create challenges to send to any electronic cutting machine. It would be ideal if you refer to the links below for additional data on the highlights included in the designer release schedule. ultramon activatecity current version of is always supported for general use. It would be ideal if you would refer to the links below for additional information on the programming features in Designer Edition Plus. Edition Plus is a different type of basic programming software that customers can access.driver easy crackboot
ReplyDeletefouad whatsapp new version has customized features with which you are able to lots of things like, able to customize ‘who can call you, ‘who can message you, even you can customize your contacts profile pictures as well as status
ReplyDeleteThanks for sharing such great content, I'm going to yo whatsapp update version This APK can be shared with my friends by logging into two accounts on the same device!
ReplyDeleteWow, what an informative article! I learned so much and can't wait to apply these tips in my own life. Local Handyman Experts
DeleteHere at Bel Air Tow Truck, we strive to provide a great towing experience, and we do not settle for less. We offer a variety of services that will allow you and your company, or family to rest assure they are getting the best rate as possible.
ReplyDeletevisit us
There are a number of applications for VPNs but I suggest
ReplyDeletehot mod VPN latest version that provides you a premium experience for free just go and download them for free
Thanks a lot for sharing this article with us
ReplyDeleteI really looking for it
Is anyone know about half up half down quick weave hair style?
Glad to found this great website. fence-companies-lincoln-ne
ReplyDeleteGreat blog. concrete-contractors-kansas-city
ReplyDeleteLooking for the best tree care service in Mission Viejo? See here: https://www.treeservicemviejo.com/
ReplyDeleteWhat a relief! Many thanks for posting these troubleshoot!
ReplyDeletehttps://www.seo-tampa.org
The Error Analysis Strategy is a strategy for gathering evidence of students' thinking, in. which the teacher presents the class with a fictitious student response to a problem and asks them to figure out what the fictitious student did wrong or was reasoning about the problem. Find out more at Orange County Tree Services
ReplyDeleteTo me, error analysis is the sweet spot for improvement visit here
ReplyDeletePlease contact my office and we can provide you with insurance for auto, home, personal umbrella, and life. We also will help protect your toys and other properties. - Amy Allstate Insurance
ReplyDeletePlease do visit my friends at Eric Jeglum Of Allstate Insurance
As Your Business Insurance Specialists we are dedicated to providing you with reliable, professional service to meet all your needs. - Work Comp Boise Insurance
ReplyDeleteOur company has been helping Treasure Valley homeowners for over 15 years. | Rain Gutter Boise
ReplyDeleteThe guidelines are as follows: 1) The error must have one significant figure; and 2) The measurement must have the same number of decimal places as the mistake. Always keep in mind that "human mistake" does not exist. If there is any uncertainty or variation, try to determine its deeper source. https://www.stampedconcretecolumbia.com/
ReplyDeleteThis is a massive and fantastic source of information. We can all contribute and profit from reading and learning from this excellent stuff. Thank you for sharing such useful information. | Sugar Land bollard installation
ReplyDeleteBest way to spot a space for improvement is to look for the error, and understand it. I was simply stating that I agree with this article. That is something that I learned from my boss, by the way, our company teaches how to get more customers from your website.
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteHey, thankyou for providing us with this information. Looking forward, to see more informative information. It is quite useful. Check out our latest manufactured machinery i.e, Shot Blasting Machine . Reach us, to know more!
ReplyDeleteI love seeing this in here and would like to read more! Coin Fraud News
ReplyDeleteAwesome post Customer Acquisition Consulting
ReplyDeleteaMAZING POST
ReplyDeletehttp://garrettlshj941.timeforchangecounselling.com/this-is-your-brain-on-sales-pipeline-automation-tampa-florida
Thanks for sharing.. sunsetter dealer near me Cherry Hill NJ
ReplyDeleteAwesome post
ReplyDeletehttp://cesarsgbp767.lowescouponn.com/10-things-steve-jobs-can-teach-us-about-direct-response-marketing-course
Thank you for this information. Great work.
ReplyDeleteconcrete Rockland
Hey, sports lover, do you want to play most popular action game Head Soccer MOD APK in your mobile, then try this out with unlimited money?
ReplyDeleteYour thoughts roused me without question. It's astonishing. I need to get familiar with your composing abilities. I likewise have a site, truth be told. In the event that you are OK, if it's not too much trouble, visit once and leave your perspective. Much obliged to you. Securities Class Law
ReplyDeleteIf you love to play card games, I would recommend to download rummy wealth apk
ReplyDelete
DeleteSearch engine optimization can bring organic traffic to your website.
Envision what's going on where we don't have even the remotest sign about the particular headcount? The mystery store relies upon your at first surveyed headcount. The last piece will be know all about reflect how much people who register by the deadline. Check for more Remote Team Holiday Activities
ReplyDeleteI like your all post. You have done really good work. Thank you for the information you provide, it helped me a lot.
ReplyDeleteVisual Web Ripper Crack
MiniTool Power Data Recovery Crack
Duplicate Photo Cleaner Crack
Nitro Pro Crack
Great post. I absolutely love this site.
ReplyDeleteProceed with the great work! discover this
We know how tough dental pain is and we want to help you as quick as possible by giving you the easy and fastest appointment available at the time you need them. - Sacramento Dentist
ReplyDeleteKindly visit our partners at Spokane Dentist | Tulsa Dentist
This comment has been removed by the author.
ReplyDeleteElectrifying! Much appreciation to you for posting that it very well may be exactly what to give motivation to somebody who needs it! Once more appreciative https://diigo.com/0pv3ju
ReplyDeleteThe site is flawlessly organized and fast to stack. It’s a noteworthy diagram of a principal WordPress subject that has been well customized. My most treasured food blog is this one. https://connerhzpm554.exposure.co/20-trailblazers-leading-the-way-in-hot-stocks-to-buy-today?source=share-connerhzpm554
ReplyDeleteIdaho Falls offers multiple arrays of dental procedures all for our patient's needs. Contact us and book your early appointment.
ReplyDeletePop To Our Website
You should see a dentist regularly to keep your teeth and gums in good health. Visiting a dentist regularly will prevent you from developing dental problems. - More Here
ReplyDeleteI like to read it. Great effort by the author, really appreciative work. www.insulationcoquitlam.com
DeleteIf you are racing games lover, I would recommed to download need for speed no limits mod apk
ReplyDeleteGREAT POST https://www.fxstat.com/en/user/profile/rostaftdyt-487794/blog/37213635-When-Professionals-Run-Into-Problems-With-Levi-And-Korsinsky,-This-Is-What-They-Do
ReplyDeleteCopper roofing system possess a unique and beautiful appearance on your property. It offers a huge increase of home value. - Get A Quote
ReplyDeleteMeridian Professional Roofers is here to assist you and our neighbor with outstanding roof repair. We repair any sort of damage, cracks, and minor leaks. - See Services
ReplyDeleteI read an article under a similar title some time prior, however this articles quality is a whole lot better. Visit Claim Your Loss
ReplyDeleteVery interesting blog. solving all your home’s foundation problems
ReplyDeleteGreat blog. Keep up the good work. foundation repair kansas 316-285-1336
ReplyDeleteError analysis in machine learning is used to ensure that a model performing well on a static training and validation dataset is just as good in production, in addition to helping performance on your target measure.
ReplyDeleteHave a look at www.a1treeservicespokane.com
I just got to this amazing site not long ago. I was actually captured with the piece of resources you have got here. Big thumbs up for making such wonderful blog page!
ReplyDeleteDo you want to know more about Tree Removal Spokane.
Excellent weblog, great work. Thanks for this! Perfect Fitness Solutions
DeleteThis is amazing bro keep up the great work and i'll come for more awesome content soon. read: techprogeeks
ReplyDeleteI can call it the best of all sites because it gives me everything i need: best rewriter tool
ReplyDeleteAre you looking for a graphic design agency in pakistan if yes then just view Zera Creative they have reliable graphic designers who provide the creative design on time and you can get better designs visit the link for more detail.
ReplyDelete
ReplyDeleteError analysis is a useful tool for identifying areas for improvement by analyzing mistakes and identifying patterns. It provides a more detailed understanding of performance, but should be used alongside other strategies like training and feedback.
Click for more details.
This is such a great resource that you are providing and you give it away for free.
ReplyDeleteYou can also visit Bathroom Remodeling Spokane
Great and informative content. Keep sharing the good work.
ReplyDeleteYou can visit us at www.charlottesvilletree.com
Amazing article! https://esvrm.com/
ReplyDelete
ReplyDeleteYour content is a breath of fresh air. It's thought-provoking and offers a new perspective.
boston iron gate installation
Very informative! www.wolverineelectrical.com
ReplyDeleteStatic analysis traditionally focused on compiled languages since compilers had access to the Abstract Syntax Tree (AST) of the code, enabling analysis before execution. For example, the C language had the lint tool, which was based on the PCC compiler and released in 1979. case studies
ReplyDeleteThat's a great quote. Error analysis is the process of identifying and understanding the causes of errors. It is a critical step in the improvement process, as it can help to identify the root causes of problems and to develop solutions that will prevent those problems from happening again.
ReplyDeletehttps://agileonboarding.com/
Amazing! I love this post so much. Thanks a lot! www.insulationsurrey.com
ReplyDeleteBut democracy isn't a state of perfection. It has to be improved, and that means constant vigilance. custom decks
ReplyDeleteGreat work mate refrigerator repair near me
ReplyDeletei would like to say its an amazing article Overland refrigerator repairs
ReplyDeleteThis is so nice. Thank you for sharing. Appliance Services
ReplyDeleteI know this is a quality-based blog along with other stuff. cash for cars chelsea
ReplyDeleteThe depth of insight that I encountered in this article truly caught my attention and left me astounded. The friendly and relatable writing style employed by the author acted as an inviting gateway into a world of knowledge and understanding.
ReplyDeletehttps://sonnysdiamonds.com/
Are you in need of handyman services in Lethbridge, AB? A handyman company that you can trust for all your renovation and repair projects? Then look no more as you have found what you are looking for. After we understand your problem, we will prepare a free quote for you to get a feel of how affordable our prices are. Handyman Pros of Lethbridge
ReplyDeleteI'm learning a lot from you. Drywall Installation
ReplyDeleteI think this article should be required reading for everyone. It is a well-written and informative article that everyone should read.
ReplyDeleterazor mx350
Excellent blog post, keep up the great work
ReplyDeletespirit hoodies
Forex trader in UAE
ReplyDeleteForex broker in Dubai
Forex broker in UAE
Everyone should read this piece, in my opinion. Everyone should read this essay because it is beautifully written and educational. Fouad WhatsApp
ReplyDeleteMy Donald Norman favorite quote is
ReplyDelete“It's not enough that we build products that function, that are understandable and usable, we also need to build products that bring joy and excitement, pleasure and fun, and yes, beauty to people's lives.”
brooklynsprayfoampros.com
was few years ago since I first time read this !
I'm bookmarking this for future reference. http://www.drywallcontractorrichmondbc.com/
ReplyDeleteYour text underscores the significance of static program analysis in identifying defects early in the development process, and it acknowledges the limitations, such as false positives and practical challenges, associated with using these tools. Static analysis is seen as a valuable but not foolproof technique for improving code quality. https://www.therodentprofessionals.com
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteThank you for sharing this post! Resin pavement provides a smooth, seamless finish that may improve the appearance of driveways, paths, and patios. Edinburgh Resin Driveway https://lifeleadgeneration.com
ReplyDeleteAffordable SEO
ReplyDeleteIt is important to note that static program analysis tools are not a silver bullet. They can sometimes produce false positives, and they cannot detect all types of defects. Therefore, it is important to use static program analysis tools in conjunction with other testing and development practices.
This comment has been removed by the author.
ReplyDeleteThe article is excellent and quite engaging to read. I thoroughly enjoy such well-written pieces, Commercial Framing Company
ReplyDeleteIt's a amazing that I found this article, it is very helpful. click here
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteYou have a great blog! Keep on posting. Other
ReplyDeleteIndeed it is. Thanks for sharing this one. https://www.unmannedsas.com/
ReplyDeleteThank you so much for sharing your journey in that analysis. www.poseidonfishingcharters.com
ReplyDeleteIndeed it is, thank you so much for sharing this one.
ReplyDeletewww.watersoftenergurus.com
Been finding this one, glad to visit this again. Thank you. https://www.unmannedsas.com/
ReplyDeleteProfile of Ian Grey - Well done on your post, it's clear and informative.
ReplyDeleteI really love how informative this blog is, Keep on posting. www.poseidonfishingcharters.com
ReplyDeleteContent provides refreshing and informative insights. I truly value the clarity with which you explain complex topics. Thank you for sharing your expertise. I've shared your posts with others, and they also find them insightful.
ReplyDeleteGreat post. Thanks for sharing this informative one. pain clothing
ReplyDeleteYour blog posts always give me new perspectives. Thanks! Vancouver Drywall Services
ReplyDeleteSuch a great improvement! unmannedsas.com/
ReplyDeleteEnjoyed to read the article of this page, good work aboveparrhomeinspections.com
ReplyDeleteYou got it right! https://amicoglobal.com/
ReplyDeleteYour work is inspiring and informative. Thanks for sharing! https://www.concretemilton.com
ReplyDeleteYes you are right. Improvement can be done by only getting error analysis. This is must. Well, if you want help with soft washing then you must go with me.
ReplyDeleteKeep on sharing this informative blog! applicationfiling.com
ReplyDeleteI'll share this enlightening post with my friends; your contribution shines. find this
ReplyDeleteLearned a lot from this. https://www.poseidonfishingcharters.com/
ReplyDelete